What is a dark web monitoring?

In today’s digital age, the Dark Web has become a mysterious and often misunderstood corner of the internet. Hidden beneath the surface, it harbors illicit activities, cybercriminals, and an array of illegal goods and services. But what exactly is the Dark Web, and how can one navigate its murky waters safely? Enter our comprehensive guide to Dark Web monitoring.
What is a dark web monitoring?
Understanding the difference between the Deep Web and the Dark Web
To truly understand the Dark Web, it’s important to first differentiate it from the Deep Web. The Deep Web refers to any part of the internet that is not indexed by search engines. This includes private databases, password-protected websites, and various other types of content that are not accessible through traditional search methods. The Dark Web, on the other hand, is a specific subset of the Deep Web that is intentionally hidden and can only be accessed through specialized software like Tor.
The Dark Web operates on a network of encrypted connections, ensuring anonymity for its users. This anonymity makes it an attractive platform for illegal activities, such as drug trafficking, hacking, and the sale of stolen data. It is important to note that not all activities on the Dark Web are illegal, as it also provides a platform for whistleblowers and activists to communicate anonymously.
The risks associated with the Dark Web
The Dark Web presents numerous risks to both individuals and businesses. For individuals, personal information can be bought and sold on the Dark Web, leading to identity theft, fraud, and compromised financial accounts. It is not uncommon to find social security numbers, credit card information, and login credentials being offered for sale by cybercriminals.
Businesses are also at risk on the Dark Web. Confidential company data, trade secrets, and intellectual property can be exposed and sold to competitors or used for extortion. Furthermore, the Dark Web provides a marketplace for cybercriminals to offer their services, such as launching DDoS attacks or distributing malware, which can have devastating consequences for a business’s operations and reputation.
Importance of Dark Web monitoring for individuals and businesses
Given the risks associated with the Dark Web, monitoring its activities becomes crucial for both individuals and businesses. By actively monitoring the Dark Web, individuals can be alerted if their personal information is being traded or used for fraudulent activities. This allows them to take immediate action to protect themselves, such as changing passwords, canceling credit cards, or contacting relevant authorities.
For businesses, Dark Web monitoring plays a vital role in protecting sensitive data and preventing cyberattacks. By monitoring the Dark Web, businesses can identify potential threats before they materialize, allowing them to take proactive measures to prevent data breaches and safeguard their reputation. Additionally, Dark Web monitoring can provide valuable intelligence on emerging trends and techniques used by cybercriminals, enabling businesses to stay one step ahead of potential threats.
Goals and methods for Dark Web monitoring
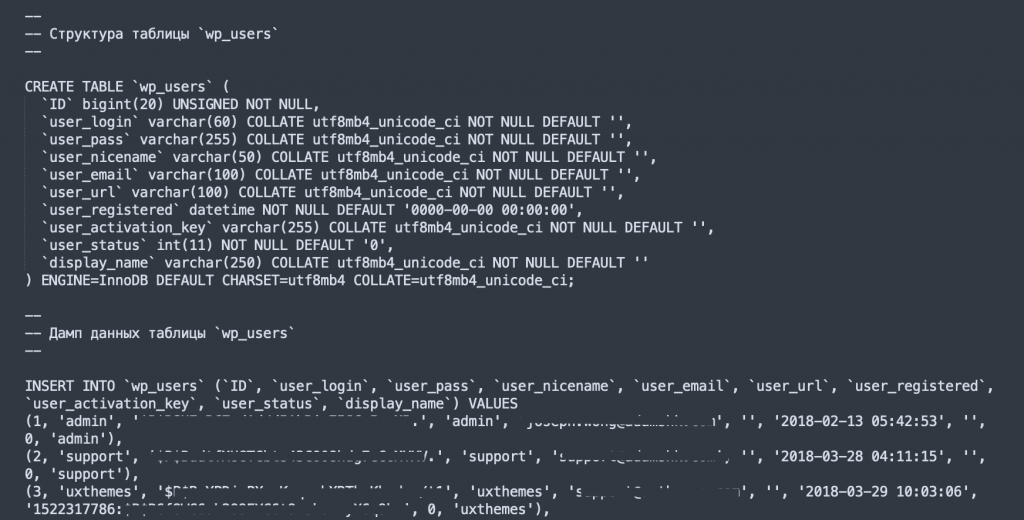
Monitoring the Dark Web requires specialized tools and techniques to navigate its hidden depths. One of the most commonly used tools is Tor, which allows users to access the Dark Web anonymously. Tor routes internet traffic through a network of volunteer-operated servers, making it difficult to trace back to the user’s original IP address. In addition to Tor, there are various Dark Web monitoring tools and services available that can help individuals and businesses detect potential threats. These tools utilize advanced algorithms and machine learning to scan the Dark Web for specific keywords, patterns, or indicators of compromise.
In principle, Dark Web Monitoring has two goals:
- Better understand the damage of past attacks.
- Detect and avert attacks in the preparation phase.
We want to explain the defence against attacks a little better. In order to fend off an attack, extended risk scenarios must be considered.
- Defence against unauthorised logins: For most, darknet monitoring means tracking down stolen user accounts. These stolen accounts could be used to illegally log in to VPN, webmail or other services. However, this is the least important part, as with a sufficient security concept (frequent change of passwords, 2FA authentication, etc.), such attacks can be technically well intercepted.
- Detection of phishing preparations: Before a phishing attack is carried out, HAckers usually reserve similar domains. This is called typosquatting. Monitoring the domains is therefore also an integral part of such a defence.
- Defence against hacking attacks on the infrastructure: If certain exploits or vulnerabilities on the clients’ servers are discussed in hacker forums, a successful attack will only be a matter of time. Thus, one must monitor the forums for such discussions, but also monitor vulnerabilities in platforms such as Shodan and Co.
There are many other reports. For this reason, you will also find a subdivision of the basic functions in Kaduu.
Setting up a Dark Web monitoring strategy
To effectively monitor the Dark Web, it is essential to have a well-defined strategy in place. This strategy should outline the specific goals of monitoring, the resources required, and the key indicators to be monitored.
Firstly, it is important to determine the scope of monitoring. For individuals, this may involve monitoring for the sale of personal information or any mentions of their name or contact details. For businesses, the scope may extend to monitoring for mentions of the company name, products, or other sensitive information.
Next, it is crucial to select the right tools and services for monitoring. Choosing tools that offer comprehensive coverage and real-time alerts can greatly enhance the effectiveness of Dark Web monitoring efforts. It is also important to regularly update and test these tools to ensure they are providing accurate and timely information.
Key indicators to monitor on the Dark Web
When monitoring the Dark Web, there are several key indicators that individuals and businesses should pay attention to. These indicators can provide valuable insights into potential threats and emerging trends.
One important indicator is the sale of personal information, such as social security numbers, credit card details, or login credentials. Monitoring for mentions of this information can help individuals detect if their personal data is being traded on the Dark Web.
Another indicator to monitor is the sale of company data or intellectual property. By monitoring for mentions of the company name, product names, or any sensitive information, businesses can identify if their data is being exposed or sold on the Dark Web.
Additionally, monitoring for discussions or advertisements related to hacking services, malware, or DDoS attacks can provide insights into potential threats targeting individuals or businesses. By detecting these indicators early on, proactive measures can be taken to prevent cyberattacks.
Dark Web Monitoring pricing 2023
The first thing that is usually associated with darknet surveillance is the high prices in relation to the benefits. If you don’t see valuable information in the monitoring, it may mean that the monitoring solution is not working well or that there are no threats at the moment. For this information, however, it is difficult to pay six-figure sums per year. One reason for the high prices in the market is that many providers also purchase their data feeds and have to pass on the high purchase prices. Kaduu’s business mission is to offer the best darknet monitoring solution on the market at the lowest possible prices. It is our understanding that every business, no matter how small, has a right to get information about threats and data leakage. We therefore make a promise: You will not find a provider who offers a better price for the same services. If you do, we will refund the price difference to you at the time of purchase. With guarantee!
Conclusion: Taking proactive steps to protect yourself and your business
In conclusion, the Dark Web is a hidden world that poses significant risks to both individuals and businesses. However, with the right tools, strategies, and monitoring services in place, it is possible to detect potential threats and prevent cyberattacks before they happen.
By understanding the difference between the Deep Web and the Dark Web, recognizing the risks associated with the Dark Web, and implementing a proactive Dark Web monitoring strategy, individuals can protect their personal information and businesses can safeguard their sensitive data.
Remember, the shadows of the internet do not have to consume you. Armed with knowledge and the right tools, you can navigate the Dark Web safely and take proactive steps to protect what matters most. So, embrace the challenge, unmask the secrets, and stay one step ahead of the cybercriminals on the Dark Web. Kaduu is here to protect your company.